CyberStrike - Global ECCO

The Game
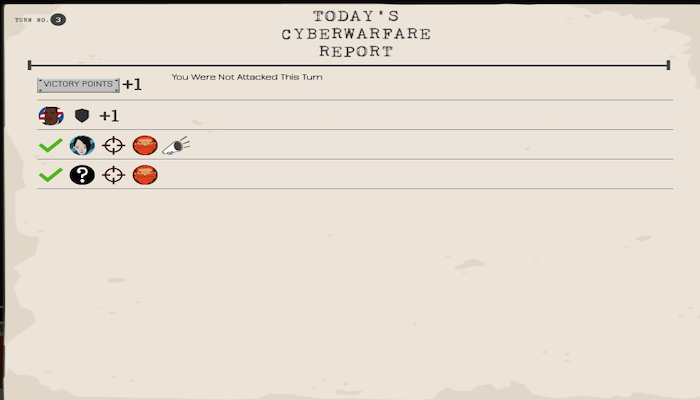
CyberStrike is a six-player game that simulates the complex strategic environment of cyber conflict. Players can play as criminals, terrorists, hackers, or different types of state actors, with each role having different capabilities and goals. Players have to consider how their offensive capabilities match up with their adversaries' defensive capabilities, and vice versa; whether to attack opponents or defend against them; whether to retaliate against attacks, particularly if the perpetrator is unknown; whether to invest in offense, defense, or detection capabilities; whether to ally with others; whether to share information or not; and how they can deter future attacks. The game is intentionally designed for thinking about the macro, strategic decisions in the cyber world. It does not require or teach any technical aspects of cyber conflict.
Roles
Criminal Organization - Download Here
Terrorist - Download Here
Hacker - Download Here
Reputable State - Download Here
How To Play
1) Players choose which role they would like to play, which will determine their starting capabilities and how they earn Victory Points.
2) Players invest three points into their capabilities either secretly or publicly.
3) Players attack other players; defend against attacks; or invest further into their capabilities, until one player reaches 20 Victory Points. Players are then ranked based on how many Victory Points they earned during the game.
Winning Conditions
A player wins by amassing points rather than by defeating a particular adversary. This design rewards a range of activities: striking the right balance between offensive, defensive, and deterrent strategies and capabilities; choosing where to invest resources; intelligence gathering; alliance building; and managing communications. The game is designed to encourage thinking about cyber space at the strategic level rather than the technical/tactical level, and does not require or teach any technical aspects of cyber conflict.
PLAY NOW