Dark Networks - Global ECCO
The Game
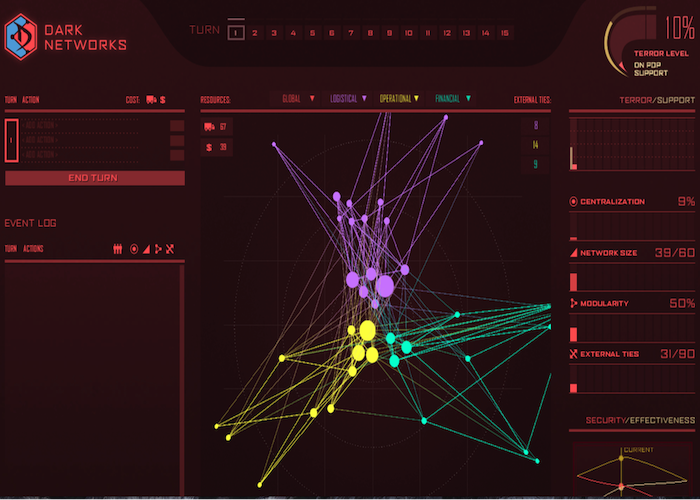
The Dark Networks game focuses on the organizational structure of terrorist groups and how these structures can be altered to make the terrorist group more or less effective. It reinforces ideas from the field of social network analysis (SNA). It is a two-player, strategic game between the state and the terrorist. Each player may have a strategy to defeat the other, but they must adapt their strategies over time to maximize their advantages.
Concepts from SNA: This game reinforces several key concepts from social network analysis: nodes and links, and the importance of size, centrality, and external ties.
Security/Effectiveness Tradeoff: The core tradeoff in this game is between security and effectiveness for the terrorist group. Measures taken to increase effectiveness (growing, centralizing) will diminish the terrorist group's security, and vice versa. This forces players to think about which attribute (security or effectiveness) they wish to maximize. This will change depending on the timing in the game and players' strategies.
The core tradeoff for the State is applying limited resources to detection or prevention and the optimal time to invert those tradeoffs.
Roles
- State
- Terrorist
How to Play
The core tradeoff in this game is between security and effectiveness for the terrorist group. Measures taken to increase effectiveness (growing, centralizing) will diminish the terrorist group’s security, and vice versa. This forces players to think about which attribute (growth or centralization) they wish to maximize. This will change depending on the timing in the game and the players’ strategies.
While the terrorist player sees the entirety of the terrorist network, the state player sees only a few nodes to begin the game. The state can gather intelligence to learn more about the network and reveal more nodes and links. The state can also deny resources to the terrorist, kill/capture specific nodes, deny the terrorist’s popular support, and increase its security presence to mitigate the effects of terrorist attacks. This game highlights the dilemmas of a state operating with incomplete information and limited options.
Winning Conditions
Victory is determined by the overall terror level. The terrorist (red) player can take several types of actions to change the structure of the network and/or the activities it engages in. It can grow or shrink, centralize or decentralize, conduct attacks, increase its popular support, and gather resources that are necessary to conduct attacks.
PLAY NOW